FECCNA Flashcards
(273 cards)
What is a characteristic of a fault tolerant network?
A network that recovers quickly when a failure occurs and depends on redundancy to limit the impact of a failure.
What is a benefit of using cloud computing in networking?
Network capabilities are extended without requiring investment in new infrastructure, personnel, or software.
What is the function of the shell in an OS?
It interfaces between the users and the kernel.
Which connection provides a secure CLI session with encryption to a Cisco switch?
An SSH connection.
A network technician is attempting to configure an interface by entering the following command: SanJose(config)# ip address 192.168.2.1 255.255.255.0. The command is rejected by the device. What is the reason for this?
The command is being entered from the wrong mode of operation.
Which communication tool allows real-time collaboration?
Instant messaging.
A host is accessing a Eb server on a remote network. Which three functions are performed by intermediary network devices during this conversation? (Three options.)
- Regenerating data signals. - Applying security settings to control the flow of data. - Notifying other devices when errors occur.
An administrator uses the Ctrl-Shift-6 key combination on a switch after issuing the ping command. What is the purpose of using these keystrokes?
To interrupt the ping process.
Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator uses a console connection to connect to the switch, which password is needed to access user EXEC mode?

linevtyin
Refer to the exhibit. From which location did this router load the IOS?

Flash memory
Refer to the exhibit. Which action will be successful?

PC2 can send a ping to 192.168.1.1.
Which connection provides a secure CLI session with encryption to a Cisco network device?
An SSH connection.
Refer to the exhibit. An administrator is trying to configure the switch but receives the error message that is displayed in the exhibit. What is the problem?
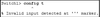
The administrator must first enter privileged EXEC mode before issuing the command.
On which switch interface would an administrator configure an IP address so that the switch can be managed remotely?
VLAN 1
What protocol is responsible for controlling the size of segments and the rate at which segments are exchanged between a web client and a web server?
TCP
What is an advantage to using a protocol that is defined by an open standard?
It encourages competition and promotes choices.
What are two benefits of using a layered network model? (Two options)
- It assists in protocol design. - It prevents technology in one layer from affecting other layers.
Which two OSI model layers have the same functionality as two layers of the TCP/IP model? (Choose two.)
- network - transport
Which name is assigned to the transport layer PDU?
segment
A network administrator is troubleshooting connectivity issues on a server. Using a tester, the administrator notices that the signals generated by the server NIC are distorted and not usable. In which layer of the OSI model is the error categorized?
physical layer
A network administrator is measuring the transfer of bits across the company backbone for a mission critical financial application. The administrator notices that the network throughput appears lower than the bandwidth expected. Which three factors could influence the differences in throughput? (Choose three.)
- the amount of traffic that is currently crossing the network - the type of traffic that is crossing the network - the latency that is created by the number of network devices that the data is crossing
What is a characteristic of UTP cabling?
cancellation
What are two characteristics of fiber-optic cable? (Choose two.)
- It is not affected by EMI or RFI. - It is more expensive than UTP cabling is.
What is a characteristic of the LLC sublayer?
It places information in the frame allowing multiple Layer 3 protocols to use the same network interface and media.




























